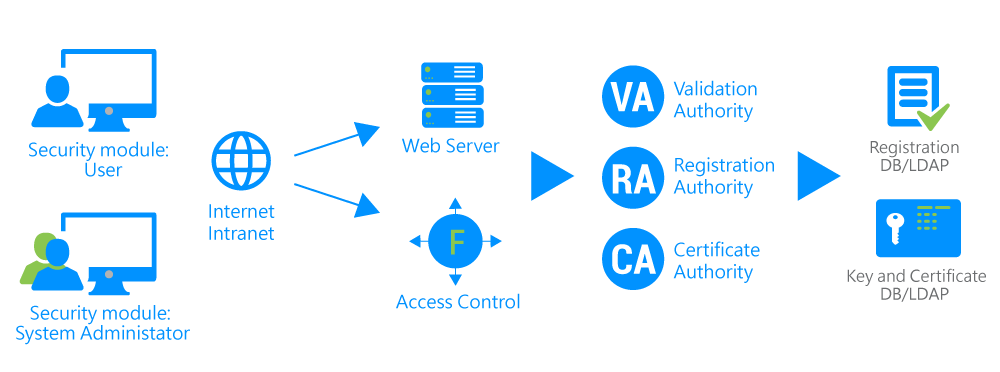
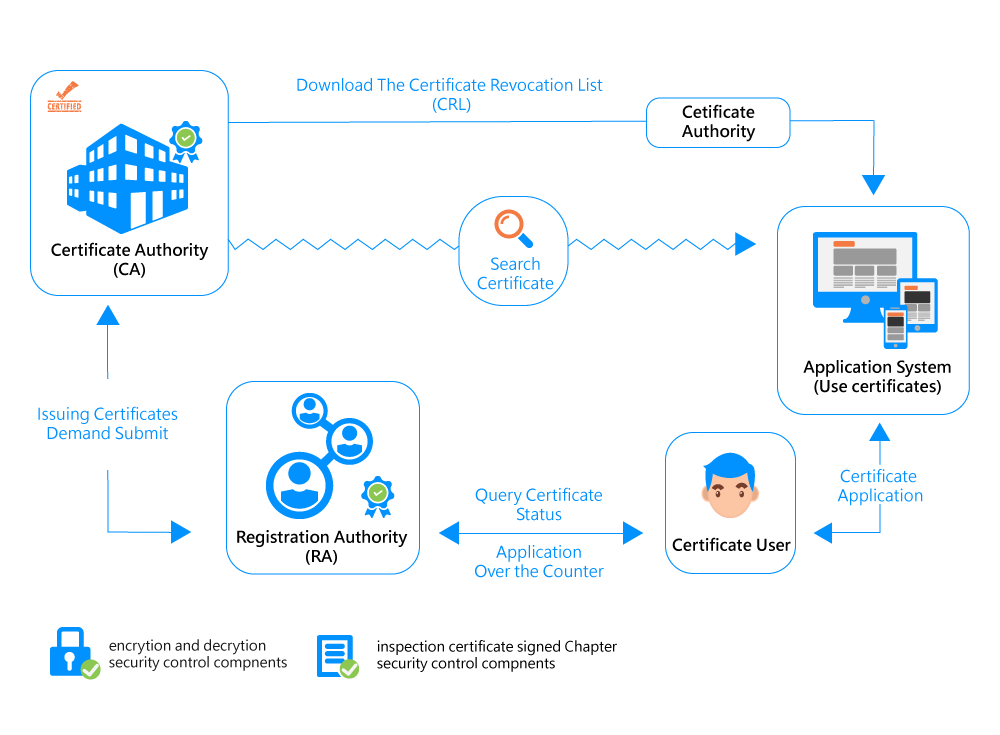
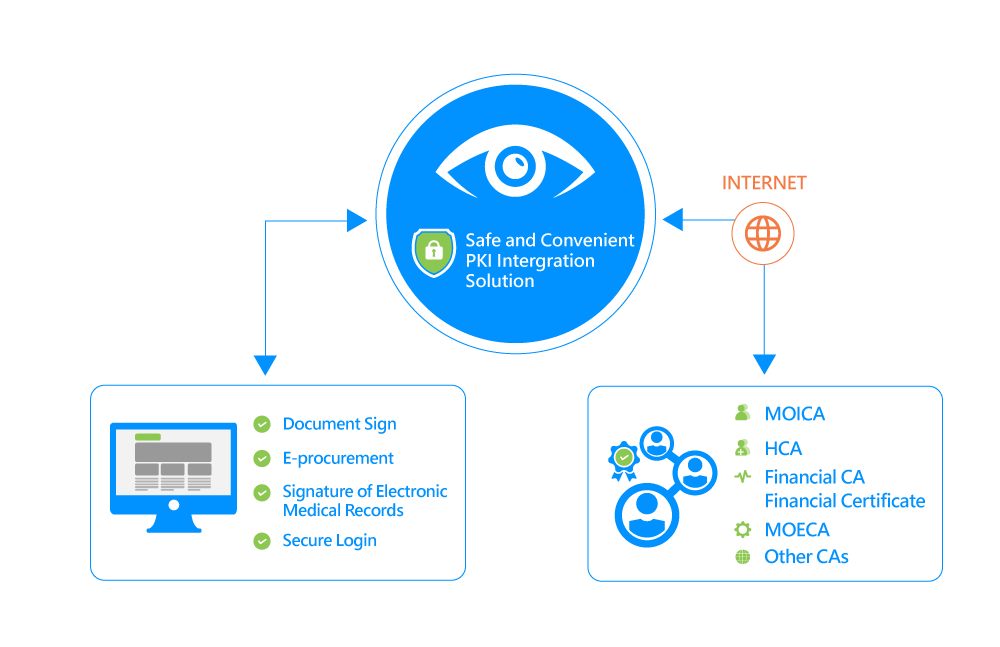
The PKI series of products are designed to meet the requirements of information security on the Internet, intranet and extranet. The goal is to build up a robust foundation of enterprise information security applications for ID control, electronic signature and data confidentiality. The Changingtec PKI places more attention on "simplified implementation of security control systems", "reduced management overhead", and "extended information security application scope" that may affect the core competence of enterprises. It provides both security control packages and tailored services to enhance business competitiveness, lower development costs required by security control systems, and enhance core values of business entities.